U.S Department of State 2018 human rights report on Algeria
The U.S Department of State released on March the 13th its annual report on the situation of human rights around the world. The report covers the period from January 1st to December 31st, 2018. According to the 2018 report, the… Keep Reading

Algeria: after the coup d’état comes the propaganda
The regime has launched a counter-offensive to divide the Algerian people since the appointment of Bedoui and Lamamra, here’s how. Fake news sponsored by general Nezzar’s son Algerie Patriotique, a media outlet owned by general Nezzar’ son, who is currently… Keep Reading

Tunisian journalist arbitrarily prevented from entering Algeria
The National Union of Tunisian Journalists (SNJT) denounced the expulsion of Tunisian journalist Intissar Chelly on Tuesday 12th March, by the Algerian authorities, who prevented her from entering the country and interrogated her for hours. In a statement issued this… Keep Reading

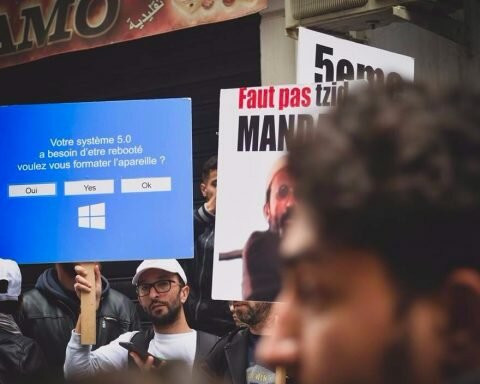
Is Algeria heading towards martial law?
The former president of the Rally for Culture and Democracy (RCD), Said Sadi, told Liberte Algerie today that “nothing is gained” with regard to the ongoing mobilization against the fifth term and the departure of the system. “I think the… Keep Reading

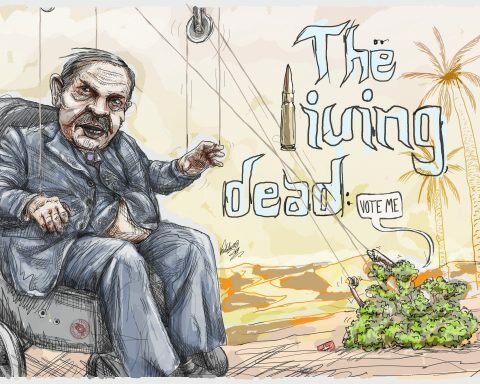
Abdelaziz Bouteflika will become an illegitimate president on the 28th of April
Strongly contested by the street, President Bouteflika has decided to con the Algerian people by overriding the provisions of the Constitution to cancel the presidential election of April 2019 and offer himself an extended mandate. A real coup against the… Keep Reading

America tells the Algerian regime: “respect the will of your people”
The United States reacted on Tuesday to the decision of the Bouteflika clan to postpone the presidential election and not run for a fifth term. Washington has expressed support for a political process in Algeria “that respects the will of… Keep Reading
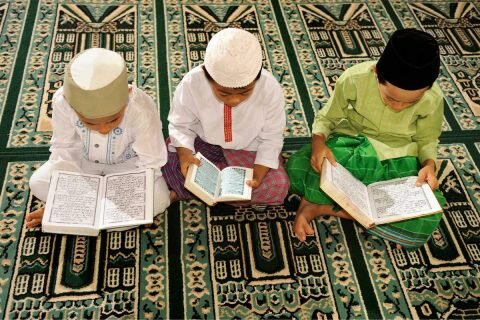
Married imam arrested for sexually abusing an underage girl
The Royal Gendarmerie of Irherm, in the province of Taroudant, 440 kilometers south of Rabat (Morocco), arrested an imam yesterday for the rape of an underage girl, reported several Moroccan media outlets. The rape goes back to last February when… Keep Reading

In despotic fashion, the Bouteflika clan cancels election to cling on to power
As suggested yesterday by the Algiers Herald, Algeria’s dictatorial regime has opted for the postponement of the election without setting a timeline for the next election, which will likely result in Bouteflika remaining president until his death. Some have come… Keep Reading